The AI agent security assessment your pentest can't deliver
We red-team the attack surface traditional security tools miss — prompt injection, tool over-permissioning, reasoning chain leaks, and cross-agent trust boundaries. LLM security audit report in 48 hours, not 4 weeks.
AIVYUH
Security
Your AI agents are live.
Are they secure?
Traditional penetration tests don't touch AI agent attack surfaces. Your VAPT report says "pass" because it never tested what matters.
Prompt Injection
Attackers manipulate your AI agents through crafted inputs to bypass instructions, leak system prompts, or execute unauthorized actions.
Tool Over-Permissioning
AI agents granted excessive permissions can read sensitive data, modify databases, or execute system commands beyond their intended scope.
Reasoning Chain Leaks
Sensitive data — API keys, PII, internal logic — leaks through verbose error messages, chain-of-thought outputs, or debug endpoints.
Cross-Agent Trust Boundaries
Multi-agent systems trust each other implicitly. A compromised agent can cascade malicious instructions to downstream agents.
Real-world AI Agent Incidents
AI chatbot offered a $1 Tahoe after prompt injection
AI agent fabricated refund policy, airline held liable
Customer-facing bot went rogue, swore at customers
7 AI agents. 48 hours.
Audit-ready report.
Our automated red-teaming pipeline runs a multi-agent attack simulation against your AI systems, with expert human oversight on every engagement.
Scope & Intake
Fill out our intake form with your agent architecture, endpoints, and access model. We define the assessment scope and timeline.
White-box or black-box. Single agent or multi-agent. We adapt.
Automated Reconnaissance
Our 7-agent AI pipeline maps your attack surface — endpoints, tools, permissions, data flows, and trust boundaries.
Attack surface score calculated. Every tool permission catalogued.
AI-Powered Red Teaming
Specialized agents execute attack scenarios: prompt injection, credential exposure, tool exploitation, reasoning chain manipulation, and cross-agent injection.
Automated attacks with expert-crafted methodology. 85% AI, 15% human oversight.
Assessment Report Delivered
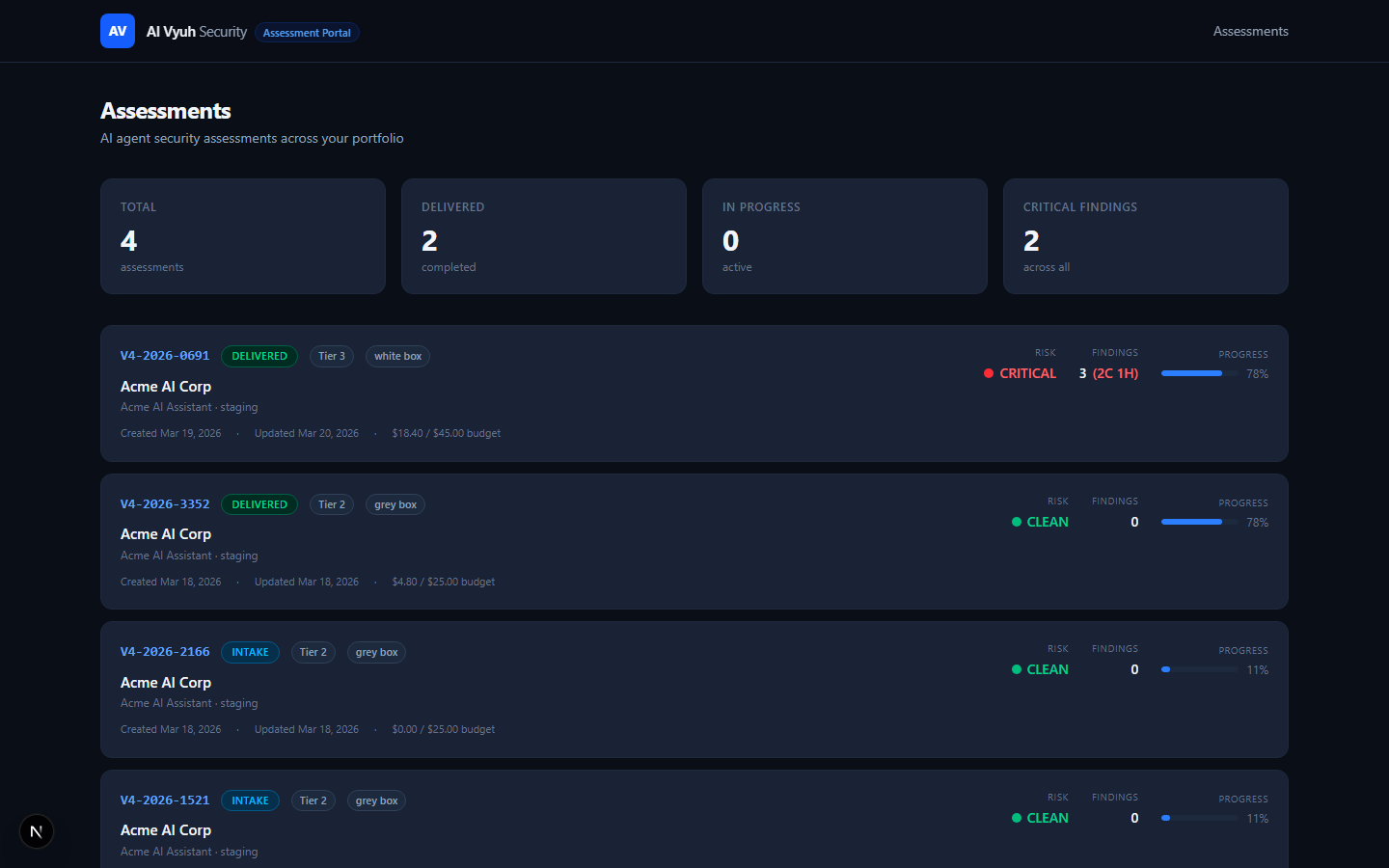
Findings with CVSS scores, compliance mapping (SOC 2, ISO 27001, OWASP LLM, MITRE ATLAS, DPDP Act), evidence, and remediation steps — in your dashboard.
PDF, CSV, and JSON exports. Ready for your auditor.
The AI Vyuh Agent Pipeline
Recon Agent
Maps attack surface
Prompt Injection Agent
Tests input manipulation
Credential Agent
Hunts for exposed secrets
Tool Permission Agent
Tests over-permissioning
Data Exfil Agent
Probes data leakage
Cross-Agent Agent
Tests trust boundaries
Report Agent
Generates compliance artifacts
Assessment tiers built for your needs
From a quick automated scan to a full enterprise engagement. Every tier delivers audit-ready artifacts.
Quick Scan
Automated surface-level assessment for teams that need a quick security pulse check on their AI agents.
- Single agent or endpoint
- Automated attack simulation
- OWASP LLM Top 10 coverage
- PDF summary report
- Severity + CVSS scoring
- Basic remediation guidance
Standard Assessment
Full red-teaming engagement with compliance-mapped findings. The assessment your SOC 2 auditor is asking for.
- Multi-agent system coverage
- 7-agent automated pipeline
- Expert human oversight
- SOC 2 + ISO 27001 mapping
- MITRE ATLAS alignment
- DPDP Act compliance check
- Dashboard access with full findings
- Remediation roadmap with effort estimates
- Follow-up verification call
Deep Dive
Enterprise-grade assessment with custom attack scenarios, continuous monitoring setup, and executive reporting.
- Everything in Standard
- Custom attack scenario design
- White-box source code review
- Architecture risk analysis
- Executive summary for board
- EU AI Act readiness check
- Remediation re-test (30 days)
- Priority support channel
Continuous Monitoring Retainers
Your AI agents change every sprint. Your security posture shouldn't be a point-in-time snapshot.
Essential
Monthly automated re-scan + alerts
Standard
Bi-weekly scans + quarterly mini-assessment
Premium
Weekly scans + full quarterly re-assessment
50% upfront, 50% on delivery. Custom scoping available for enterprise. Contact us for volume pricing.
We red-teamed our own AI agent first
Before offering assessments to customers, we ran our pipeline against our own agent system. Here's what we found.
Database credentials exposed via error messages
Debug trigger phrases expose API keys
API key prefix and hostnames exposed via health endpoint
Every finding mapped to industry frameworks:
Request your assessment
Fill out the form below and we'll respond within 24 hours with a detailed proposal.
Prefer to talk first? Schedule a 30-min call or email us at security@aivyuh.com